Overview
Assumptions
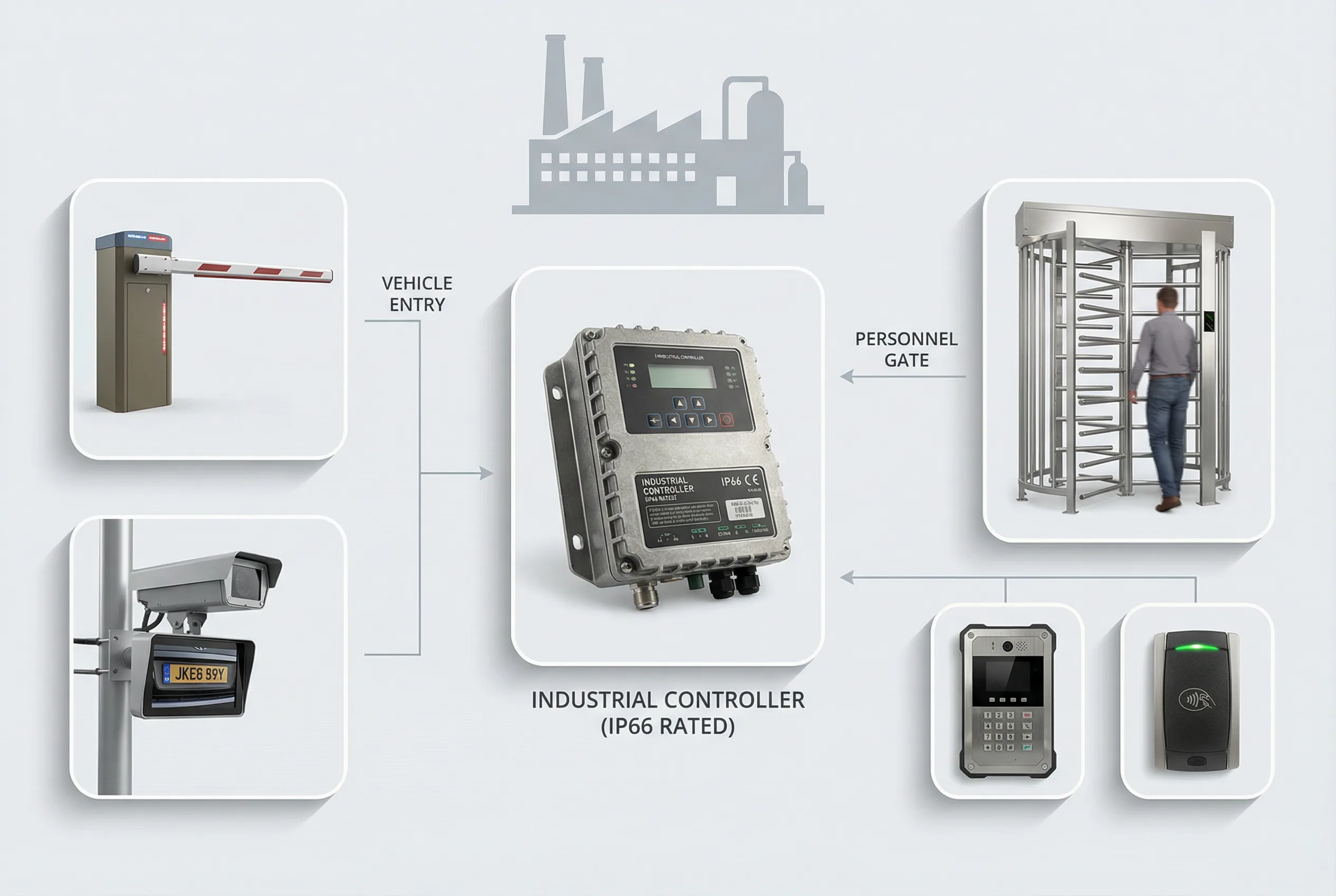
Suitable for manufacturing plants, industrial parks, logistics centers, and production facilities, targeting factory security managers, production management teams, and industrial integrators.
Core Value
Solves the problem of complex personnel types, difficult vehicle-pedestrian coordination, and high production area security requirements.
Avoids unauthorized entry into production areas, unclear contractor management, and inability to coordinate with attendance systems.
Provides layered access control for different zones, real-name management, and production safety boundary protection.
Guide Structure
Product Overview
What is this solution?
Factory access control must address multiple personnel types (employees, contractors, visitors, drivers), multiple zone types (office, production, warehouse, restricted), and multiple time patterns (shifts, overtime, maintenance windows). The core challenge is not the technology itself, but establishing a permission model that matches production management logic and can be maintained long-term.
Key Capabilities
Zone-based Layered Access Control
Different zones have different access requirements and authentication methods.
Multi-type Personnel Management
Supports employees, contractors, visitors, and vehicle-related personnel with different permission models.
Shift & Time-based Access
Access permissions are linked to shift schedules and production time windows.
Attendance Integration
Access events feed into attendance management for production workforce tracking.
Value by Role
Zone boundaries must be clear and enforced; access control is the primary tool.
Access control supports production safety and workforce management, not just security.
Integrated access and attendance reduces duplicate management.
Factory projects require understanding of production logic, not just access control technology.
Selection Method
Selection Framework
Use the following decision steps to determine if this solution fits your project. Each step narrows the selection scope and identifies key risk areas.
First map all personnel types and zone requirements before selecting equipment.
Shift-based access requires platform support for time-window permissions.
Contractor management needs visitor-access linkage, not just a separate visitor system.
When budget is limited, prioritize restricted zone access control over general office areas.
Quick Decision Rules
If your project has more than 3 sites or 100+ door points, prioritize platform scalability over device cost.
If personnel turnover is high, ensure the permission revocation workflow is automated, not manual.
If the area is high-security (server room, pharmacy), require dual-factor authentication as a minimum.
If integration with HR or attendance systems is required, verify API compatibility before procurement.
Application Scenarios
Applicable Scenarios
Manufacturing plants with multiple production zones
Industrial parks with mixed use areas
Logistics centers with vehicle and pedestrian coordination
Facilities with contractor and visitor management needs
Scenario Characteristics
Personnel Structure
Evaluate the complexity of personnel types, turnover rate, and permission granularity requirements.
Security Level
Determine authentication strength requirements based on asset value and regulatory requirements.
Growth Expectation
Consider future expansion, new sites, and system integration requirements in the selection.
Metrics & Acceptance
Key Performance Indicators
| Indicator | Minimum Standard | Enhanced Standard | Verification Method |
|---|---|---|---|
| Authentication Response Time | < 2 seconds | < 0.5 seconds | On-site timing test |
| False Rejection Rate (FRR) | < 1% | < 0.1% | 100-sample test |
| Offline Operation Duration | 4 hours | 72 hours | Power-off simulation |
| Permission Sync Latency | < 5 minutes | Real-time (< 30s) | Add/revoke timing |
| Event Log Retention | 90 days | 365 days+ | Platform query check |
| Emergency Release Time | < 10 seconds | Automatic on alarm | Fire alarm simulation |
Acceptance Checklist
Installation Conditions
Zone boundaries, door types, and cable routing must be planned with production layout.
Environment Requirements
Industrial environments (dust, temperature, vibration) require appropriate device protection ratings.
Commissioning Requirements
Must verify shift-based access, contractor workflows, and attendance integration.
Operations Requirements
Establish permission update procedures for shift changes, contractor renewals, and zone changes.
Common Pitfalls
Permission model complexity is often underestimated; start with a clear zone and role matrix before deployment.
Compare & Recommend
Tier Definition
Entry Tier
Target: Small single-site, low security requirement, limited budget
Risk: Limited scalability, manual management
Professional Tier
Target: Multi-site or medium-scale, compliance requirements, integration needs
Risk: Higher deployment complexity, requires professional integration
Enterprise Tier
Target: Large-scale, high security, multi-system integration, audit requirements
Risk: High investment, long implementation cycle
Recommended Combinations
Basic Combination
Required
- Zone access terminals and controllers
- Access management platform
- Attendance integration module
- Visitor management for contractors
Scenario: Single-site, standard security, < 50 door points
Risk: Difficult to expand later, manual permission management
Professional Combination
Required
- Zone access terminals and controllers
- Access management platform
- Attendance integration module
- Visitor management for contractors
Optional Add-ons
- Turnstiles for main entrances
- Vehicle access control
- Biometric authentication for restricted areas
Scenario: Multi-site or compliance-required, 50–500 door points
Risk: Integration complexity, requires professional deployment
Enterprise Combination
Required
- Zone access terminals and controllers
- Access management platform
- Attendance integration module
- Visitor management for contractors
Optional Add-ons
- Turnstiles for main entrances
- Vehicle access control
- Biometric authentication for restricted areas
- Video surveillance linkage
- Emergency muster module
Scenario: Large-scale, high security, full integration, 500+ door points
Risk: High investment, long implementation, requires experienced integrator
Compatibility & Integration
System Overview
The system consists of zone access terminals, controllers, locks, turnstiles for high-traffic entrances, vehicle access control, attendance terminals, access management platform, and integration with HR and production management systems.
Integration Objects
HR / Identity Management System
Sync personnel join/leave/transfer events
Video Surveillance (CCTV/VMS)
Link access events with video evidence
Visitor Management System
Automate temporary access credential issuance
Fire Alarm / BMS
Emergency release and evacuation linkage
Attendance System
Avoid duplicate card-swiping infrastructure
Elevator Control System
Extend access control to floor-level
Integration Risks & Mitigation
Protocol mismatch between controller and platform
Consequence: Events not reported, permissions not synced
Mitigation: Verify protocol compatibility before procurement; request test environment access
HR system API changes break permission sync
Consequence: Permission residuals after personnel departure
Mitigation: Use middleware or webhook-based integration; implement daily sync audit
Fire alarm release conflicts with access control logic
Consequence: Doors fail to open during emergency, evacuation blocked
Mitigation: Define fire release priority in system design; test linkage before go-live
Network latency causes offline controller permission lag
Consequence: Revoked credentials still grant access
Mitigation: Set offline permission cache TTL; implement emergency revocation mechanism
Installation & O&M
Installation Process
- 1
Personnel are enrolled with their role, zone permissions, and time windows.
- 2
Personnel authenticate at zone boundaries based on their permission level.
- 3
Controllers grant or deny access based on zone rules and time windows.
- 4
Events are recorded and fed to attendance and management systems.
- 5
Abnormal access triggers alerts for security response.
Pre-installation Risk Checklist
Confirm door frame material and lock mounting compatibility
Verify power supply capacity for all lock and controller loads
Check network connectivity and bandwidth at each door point
Confirm fire alarm integration protocol with fire system vendor
Verify cable routing path is free of interference sources
Confirm backup power (UPS/battery) runtime meets requirements
Validate reader mounting height and angle for user accessibility
Check environmental conditions (temperature, humidity, dust) for outdoor readers
Common Installation Errors
Mixing power and signal cables in the same conduit
Consequence: Electromagnetic interference causing reader malfunction
Correct Approach: Separate conduits for power and signal; maintain 30cm minimum distance
Installing readers in direct sunlight without weatherproofing
Consequence: Accelerated aging, biometric failure in high temperature
Correct Approach: Use IP65+ rated readers; add sun shade for outdoor installations
Not testing emergency release before handover
Consequence: Emergency release fails during real incident
Correct Approach: Mandatory fire alarm linkage test before project acceptance
O&M Monitoring & Maintenance
| Item | Frequency | Action |
|---|---|---|
| Door lock mechanical check | Monthly | Test lock/unlock force, check alignment |
| Controller communication status | Weekly | Check online status in platform dashboard |
| Backup power battery capacity | Quarterly | Simulate power outage, verify runtime |
| Permission audit | Monthly | Review active credentials vs. current personnel list |
| Firmware/software updates | Quarterly | Apply security patches; test in staging first |
Ready to Start Your Project?
Contact our solution team for expert access control selection advice and quotation.
